Linux Perimeter Security
Secure Your Linux Perimeter. Scan. Detect. Respond.
A self-hosted Linux security platform that combines vulnerability scanning, intrusion detection, and canary deployment. Know when attackers probe your network, exploit your systems, or access sensitive files.
Real-time monitoring/ Self-hosted/ Easy to deploy
app.tomespell.com/dashboard
Capabilities
Everything You Need to Defend Your Perimeter
Three integrated capabilities in a single self-hosted platform. Deploy once, protect everywhere.
Vulnerability Scanning
Continuously scan your Linux hosts for known vulnerabilities and system weaknesses. Prioritize remediation with severity-ranked findings.
- Automated CVE detection across packages
- System weakness enumeration
- Severity-based prioritization
- Scheduled and on-demand scans
Intrusion Detection
Monitor process execution, file access, and network connections in real-time using eBPF. Detect suspicious activity the moment it happens.
- eBPF-based process and file monitoring
- Real-time network connection tracking
- Active response against AI-driven intrusion attempts
- Configurable alerting via email, Slack, and webhooks
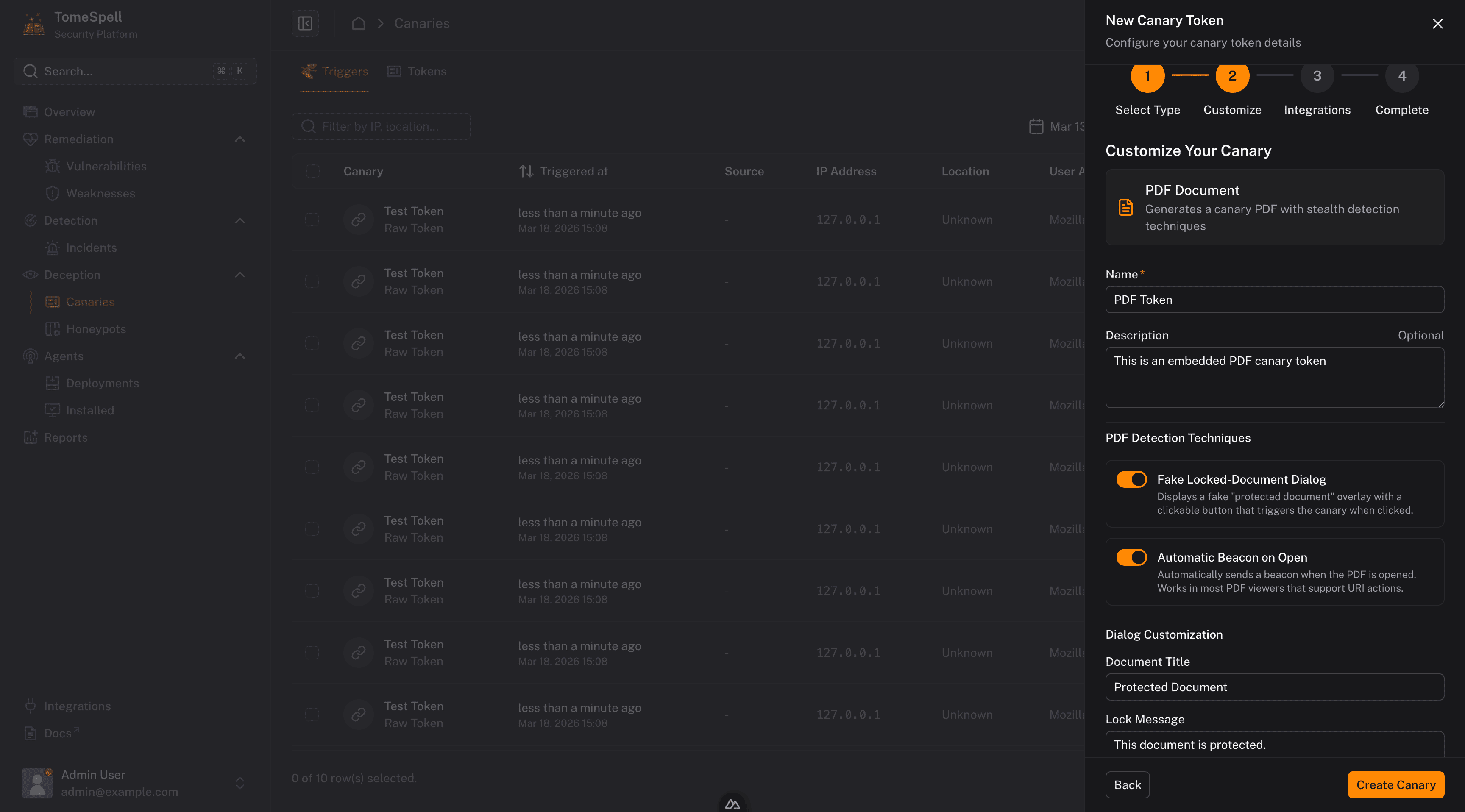
Canary & Honeypot Deployment
Deploy decoy services and trackable documents that alert you when accessed. Turn your network into a minefield for attackers.
- SSH, HTTP, and TCP honeypot services
- Trackable PDF documents with access reporting
- Port scan detection on trap ports
- Hardware canary device support
How It Works
From Setup to Detection in Minutes
A simple deployment workflow that gets your infrastructure protected quickly.
Deploy
Install the controller on your server and configure the dashboard.
Configure
Set up monitored paths, scan schedules, and honeypot services.
Monitor
Agents start reporting vulnerabilities, file access, and network events.
Detect
Receive instant notifications when threats are identified.
Respond
Review detailed findings with context, severity, and remediation guidance.
Step 0 of 0
Deploy
Install the controller on your server and configure the dashboard.
Configure
Set up monitored paths, scan schedules, and honeypot services.
Monitor
Agents start reporting vulnerabilities, file access, and network events.
Detect
Receive instant notifications when threats are identified.
Respond
Review detailed findings with context, severity, and remediation guidance.
Step 0 of 0
FAQ
Frequently Asked Questions
Everything you need to know about TomeSpell.
Ready to Secure
Your Infrastructure?
Deploy TomeSpell today and gain complete visibility into your Linux perimeter.